How to Set Up Basic Security Headers on Apache or Nginx
A beginner-friendly guide to adding common website security headers on Apache or Nginx, with notes on CSP, framing and content sniffing.
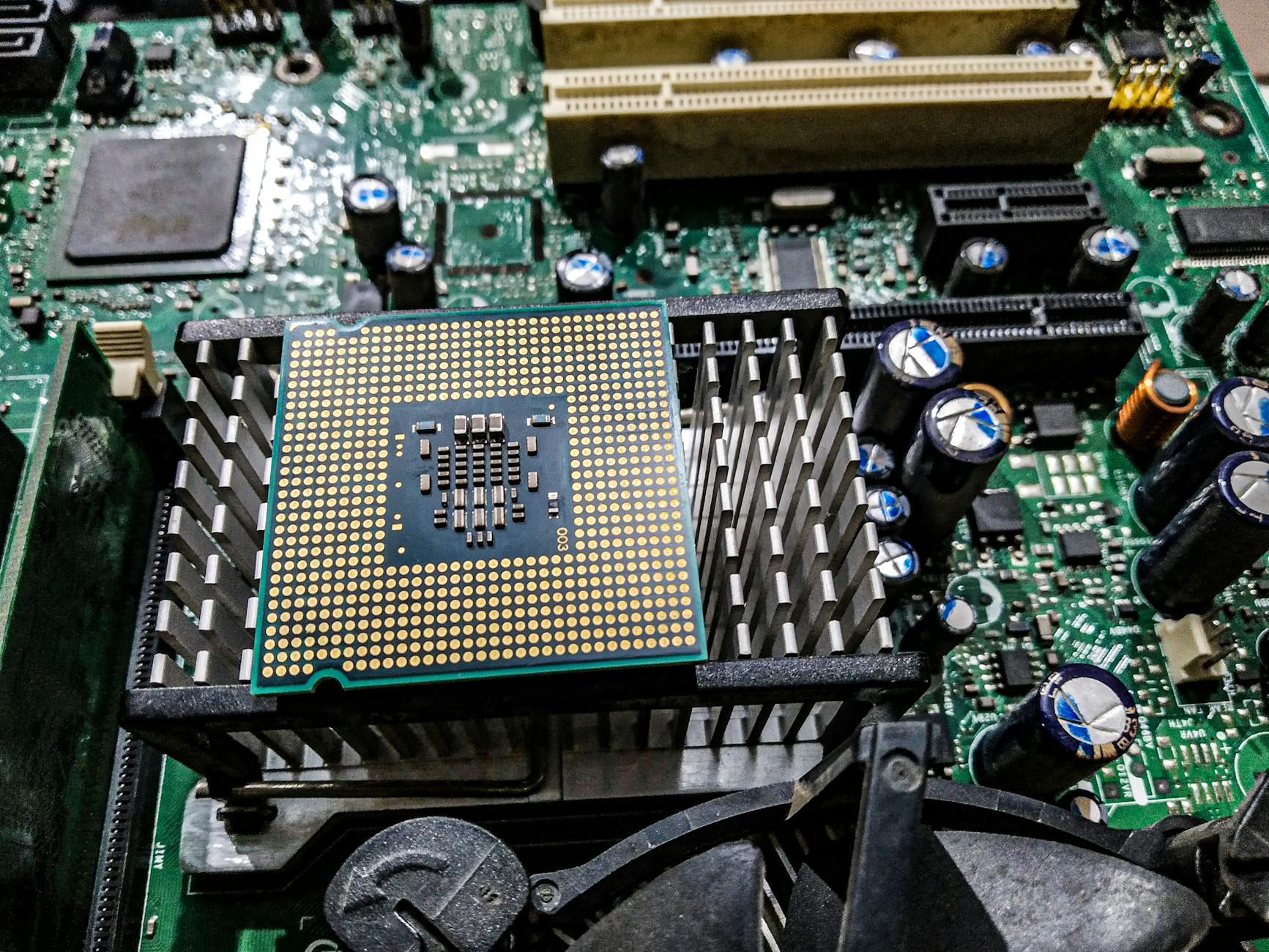
How to Diagnose High CPU Usage on a Linux Web Server
Troubleshoot high CPU usage on a Linux web server by checking processes, services, logs, traffic patterns, cron jobs and application bottlenecks.
How to Choose a VPS for WordPress, WooCommerce or a Web App
Learn how to choose the right VPS by matching CPU, RAM, storage, bandwidth, support and growth plans to your actual workload.
WordPress Maintenance Plan Checklist for Agencies and Freelancers
A complete WordPress maintenance plan checklist covering updates, backups, plugin reviews, uptime checks, security and client reporting.
How to Improve Website Uptime Monitoring for Small Businesses
Build a more useful uptime monitoring setup with health checks, alerting, SSL checks, region testing and service-level visibility.
Common Nginx Mistakes That Cause 502 Bad Gateway Errors
Learn the most common Nginx misconfigurations behind 502 Bad Gateway errors, including upstream failures, sockets, permissions and timeouts.
How to Back Up a Linux Server Properly Before Making Risky Changes
A practical guide to backing up a Linux server before major updates, migrations or configuration changes, with rollback and restore planning.
How to Reduce Spam From Contact Forms on WordPress
Cut down contact form spam on WordPress using CAPTCHA alternatives, honeypots, rate limiting, email validation and server-side checks.
How to Write a Server Hardening Policy for a Small Hosting Business
Create a practical server hardening policy for a small hosting business with patching, access control, logging, backups and configuration standards.
How to Speed Up WooCommerce Without Upgrading Your Server First
Practical WooCommerce performance improvements covering caching, themes, plugins, images, database cleanup and checkout bottlenecks.